Zero Trust: more than a concept, an essential journey to protect your company
Understand what Zero Trust is: a continuous and essential cybersecurity journey to protect your company's data.

Diego Aron Gomes
The evolution of cybersecurity and new challenges.
Cybersecurity has always been a fundamental pillar for companies. However, as we advance to hybrid models, remote work and massive cloud adoption, even basic security “hygiene” has become a major challenge.
The need to protect sensitive data, update systems and ensure business continuity is more urgent than ever. Complex environments, with expanded attack surfaces, make organizations more vulnerable to incidents and leaks.
What is Zero Trust?
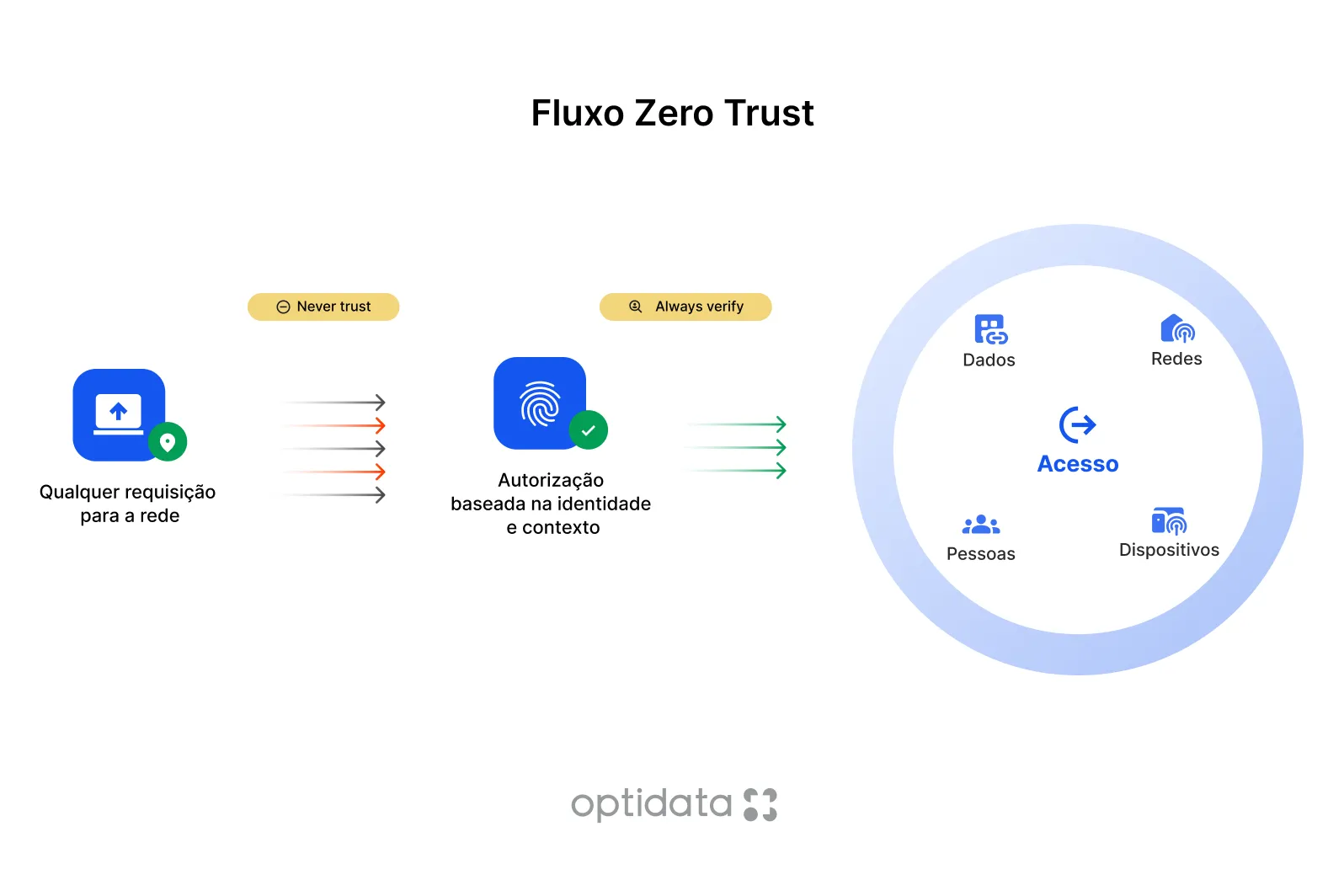
Within this context emerges the concept of Zero Trust, or “Never Trust, Always Verify”. Instead of trusting internal networks or perimeters, Zero Trust requires continuous and contextual verification, analyzing device, location, privileges and behavior.
The principle of least privilege and constant monitoring help drastically reduce the attack surface and minimize impact in case of intrusions.
A journey, not a destination
Implementing Zero Trust is not a project with beginning, middle and end. It’s a continuous journey that requires visibility over assets, clear policies and intelligent automation to balance security and user experience.

"Zero Trust is not a destination, it's a continuous path of maturation."Mauricio Canto, Product Director at iTFLEX Cybersecurity
The importance of mapping risks and processes
Data recovery and risk management are also fundamental. Attacks like ransomware have grown more than 100% in recent years, paralyzing operations and impacting reputations.
Therefore, it’s essential to map critical processes, involve senior management and regularly test recovery plans. Investing in automation and preventive security is much more effective (and economical) than paying ransoms or dealing with image damage.
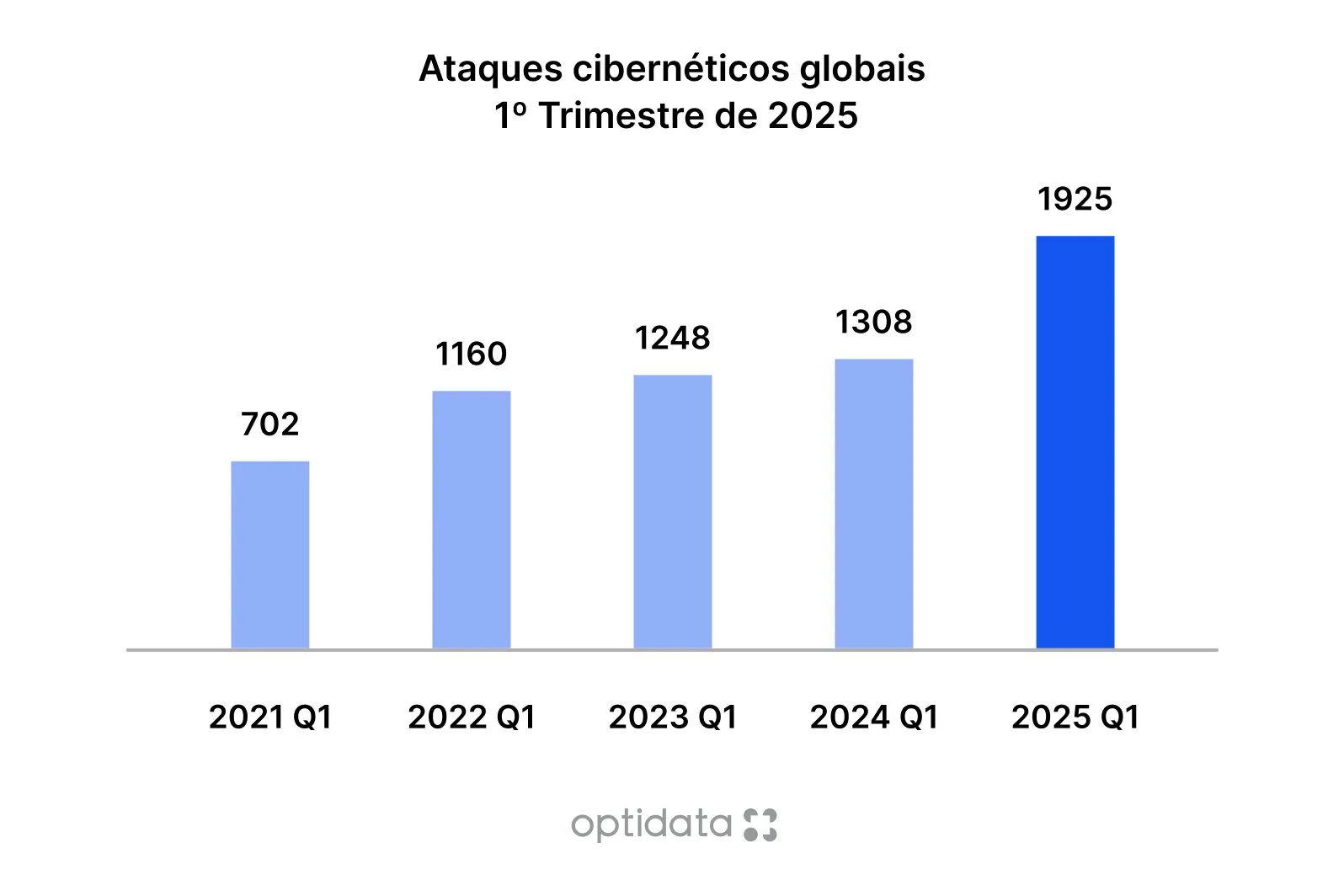 Source: Data adapted from study on increase in cyber attacks
Source: Data adapted from study on increase in cyber attacks
Awareness: the most vulnerable link
Awareness campaigns are essential, but there are still gaps in budget, dedicated teams and recurrence management. Real behavior changes depend on personalized communication, practical simulations and leadership engagement.

Next steps to adopt Zero Trust
Maturity assessment
- Identify current capabilities
- Map security gaps
- Establish a baseline
Business case construction
- Calculate security ROI
- Define success metrics
- Ensure executive sponsorship
Implementation plan
- Prioritize use cases
- Choose appropriate technologies
- Create a phased schedule
Zero Trust in practice
- Identify critical assets: map what needs priority protection.
- Create contextual policies: consider who, what, when, where and how resources are accessed.
- Apply segmentation and control: limited access to what’s necessary (principle of least privilege).
- Map access flows: understand normal patterns and detect anomalies.
- Implement continuous authentication: go beyond initial login.
- Monitor and adjust: constantly refine policies.

"Bringing Zero Trust to the reality of day-to-day operations is essential, even if the person is not directly involved in the technical part. We are all active parts of an ecosystem, and every attitude counts."Diego Aron, Head of Operations at Optidata
Zero Trust as corporate culture
Bringing the Zero Trust theme to the routine of operations, whether development, administration, cloud operations or management, strengthens the company’s privacy and confidentiality pillar.
Even those not directly involved in technical implementation need to understand the importance of the concept, correctly classifying sensitive data and recognizing different levels of information criticality.
These attitudes not only facilitate the adoption of Zero Trust culture, but also strengthen each employee’s professional profile, making them active agents in the security maturation journey.
Security culture in practice
For Optidata, security goes far beyond processes or technologies; it starts with people. That’s why the team recently went through training and a special lecture on cybersecurity and Zero Trust, focused on Support and Engineering teams. The goal was to reinforce the importance of constant attention to access, sensitive data and good practices in daily life.
By training strategic areas such as Support and Engineering, Optidata ensures that professionals who are on the front line, serving customers, resolving incidents and managing critical environments, are prepared to identify risks and act preventively. This type of initiative strengthens internal culture, reduces vulnerabilities and increases confidence in all operations.
More knowledge means more protection and more confidence. By investing in training, Optidata positions itself not only as a technology company, but as a partner committed to the security and continuity of clients’ businesses. After all, the greatest layer of defense will always be a well-trained, aligned and aware team of their role in the digital ecosystem.
Conclusion: security as strategic value
In today’s world, security cannot be seen only as a cost. It’s a strategic investment and a competitive differentiator.
Building a Zero Trust approach requires collaboration, vision and continuous commitment, but the gains in protection, resilience and reputation are invaluable.
More than ever, trust is not a starting point. It’s something to be earned and maintained every day.